devices.
“
“FreeRADIUS is the most widely deployed RADIUS server in the world. It is the basis for multiple commercial offerings. It supplies the AAA needs of many Fortune-500 companies and Tier 1 ISPs. It is also widely used in the academic community, including eduroam. The server is fast, feature-rich, modular, and scalable.” –FreeRADIUS home page
I’ve been using FreeRADIUS in production for a few years now, mostly to support wireless users. One of the benefits of FreeRADIUS — besides being open source, of course — is the numbers of backends one can use for authentication:
“If a password is not available locally for some reason, the server can pass the authentication to another system such as
LDAP,
PAM, Unix (/etc/passwd),
Kerberos,
Active Directory, or
RADIUS server via RADIUS proxying. Local programs (e.g. CGI scripts) can also be used to authenticate users via shell scripts or any other method.
Perl or
Python scripts can be pre-loaded into the server, which significantly lowers the cost of running such programs.”
Powerful, huh? Indeed.
For this demonstration, I’m installing a new CentOS 5.2 virtual machine on my
MacBook under
VMware Fusion. Installing the operating system, however, is beyond the scope of this document. Also, we’ll just be using the local system database for now — we’ll save SQL and LDAP (perhaps even Active Directory) authentication for later. After we get FreeRADIUS up and running, we’ll set up a user account and then configure a Cisco router to use RADIUS for authentication.
Let’s begin with installing FreeRADIUS by running (as root) the following command:
کد:
[root@bertram ~]# yum -y install freeradius
“yum” should have went out, grabbed the appropriates packages and dependencies, and installed them. If the end of your output looks like this, you’re all set:
کد:
Complete!
[root@bertram ~]#
Because FreeRADIUS will need to use the local system database for authentication, we need to set ‘user = root’ and ‘group = root’ in radiusd.conf. This is easy enough, just open up /etc/raddb/radiusd.conf, and change the lines that reads “user = radiusd” and “group = radiusd” to “user = root” and “group = root”, respectively. Note that this (running our daemons as root) is almost always something we want to avoid. Using other authentication backends, such as SQL or LDAP, would not require this change and would allow the FreeRADIUS service to run under the default “radiusd” unprivileged account.
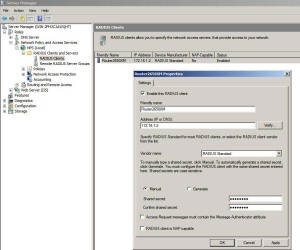
Next, we need to let FreeRADIUS know about our NAS — in this case, our Cisco router. For the sake of this demonstration, our router (R1) will have IP address 192.168.1.201. We’ll also need a shared secret that the router and RADIUS server use. Let’s use the ever popular “SECRET_KEY”. Add the following to the end of /etc/raddb/clients.conf:
کد:
client 192.168.1.201 {
secret = SECRET_KEY
shortname = R1
nastype = cisco
}
Then, on the FreeRADIUS side, we need to create a user account in the local user database that we’ll use for actually authenticating to R1. Nothing special here, just creating a new user account and setting the password. I’ve passed the plain-text password into “passwd” via stdin so that you can see it. Normally, we wouldn’t do that — just run “passwd cisco” and enter the password when prompted:
کد:
[root@bertram ~]# /usr/sbin/useradd cisco
[root@bertram ~]# echo secret | passwd --stdin cisco
Changing password for user cisco.
passwd: all authentication tokens updated successfully.
[root@bertram ~]#
We now have a local user named “cisco” with a password of “secret” that we’ll use when it comes time to authenticate to R1. Before we can do that, however, we must let FreeRADIUS know about the user. Append the following to /etc/raddb/users:
کد:
cisco Auth-Type := System
Service-Type = NAS-Prompt-User,
cisco-avpair = "shell:priv-lvl=15"
This notifies FreeRADIUS of a local user account named “cisco”. Using the “cisco-avpair” attribute in this manner allows us to automatically assign privilege level 15 to the user, removing the requirement for the user to issue “enable” (and the enable secret) in order to gain elevated access.
Let’s get started configuring R1. I’m going to assume that you’re starting from a default configuration. The first thing we want to do is create a “fallback” user account (on the router itself) that we can use to authenticate if, for some reason, connectivity to the RADIUS server is lost. Let’s create a user named “admin” with a password of “letmein”:
کد:
R1(config)#username admin privilege 15 secret letmein
Under normal circumstances, we’ll never use this local account — only when the RADIUS server is unavailable.
The first thing I need to do is configure my interface on R1 and verify we can ping the RADIUS server. Assuming you already have your router up and running, you can likely skip this step:
کد:
R1(config)#interface fastethernet 3/0
R1(config-if)#ip address 192.168.1.201 255.255.255.0
R1(config-if)#no shutdown
R1(config-if)#
*Mar 1 00:10:14.635: %LINK-3-UPDOWN: Interface FastEthernet3/0, changed state to up
*Mar 1 00:10:15.635: %LINEPROTO-5-UPDOWN: Line protocol on Interface FastEthernet3/0, changed state to up
R1(config-if)#do ping 192.168.1.51
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.1.51, timeout is 2 seconds:
.!!!!
Success rate is 80 percent (4/5), round-trip min/avg/max = 4/11/24 ms
R1(config-if)#
Excellent, all set! Let’s start configuring R1 for AAA:
کد:
R1(config)#aaa new-model
R1(config)#radius-server host 192.168.1.51 auth-port 1812 acct-port 1813 key SECRET_KEY
AAA should now be enabled on R1. Note that we provided the IP address of the RADIUS server as well as the shared secret we configured in FreeRADIUS earlier. In addition, we must specify the “auth-port” and “acct-port” used by FreeRADIUS, as these are different from Cisco’s defaults (1645 and 1646). Let’s configure authentication:
کد:
R1(config)#aaa authentication login default group radius local
R1(config)#line vty 0 4
R1(config-line)#login authentication default
R1(config-line)#line con 0
R1(config-line)#login authentication default
Here, we’ve told R1 to use RADIUS for authentication and to fall back to the local user database if the RADIUS server is not available. We don’t want to DoS ourselves!
The following command will allow the user to run an “exec” shell when logging into the router:
کد:
R1(config)#aaa authorization exec default group radius if-authenticated
Last, but not least, we want accounting (the final “A” in “AAA”):
کد:
R1(config)#aaa accounting exec default start-stop group radius
R1(config)#aaa accounting system default start-stop group radius
That should be enough to allow us to login with our local (Linux) system account “cisco” that we created earlier. Let’s give it a shot:
کد:
macbook:~ jlgaddis$ telnet 192.168.1.201
Trying 192.168.1.201...
Connected to 192.168.1.201.
Escape character is '^]'.
User Access Verification
Username: cisco
Password:
R1#show ip interface brief
Interface IP-Address OK? Method Status Protocol
Ethernet0/0 unassigned YES unset administratively down down
Ethernet0/1 unassigned YES unset administratively down down
Ethernet0/2 unassigned YES unset administratively down down
Ethernet0/3 unassigned YES unset administratively down down
Serial1/0 unassigned YES unset administratively down down
Serial1/1 unassigned YES unset administratively down down
Serial1/2 unassigned YES unset administratively down down
Serial1/3 unassigned YES unset administratively down down
FastEthernet3/0 192.168.1.201 YES manual up up
R1#exit
Connection closed by foreign host.
macbook:~ jlgaddis$
Success! We’ve installed FreeRADIUS, added a local user account, set up the NAS client (R1) and configured it to authenticate against the RADIUS server. Let’s take a look at what was logged by FreeRADIUS:
کد:
[root@bertram ~]# cat /var/log/radius/radacct/192.168.1.201/detail-20081119
Wed Nov 19 00:24:47 2008
Acct-Session-Id = "00000005"
User-Name = "cisco"
Acct-Authentic = RADIUS
Acct-Status-Type = Start
NAS-Port = 130
NAS-Port-Id = "tty130"
NAS-Port-Type = Virtual
Calling-Station-Id = "192.168.1.49"
Service-Type = NAS-Prompt-User
NAS-IP-Address = 192.168.1.201
Acct-Delay-Time = 0
Client-IP-Address = 192.168.1.201
Acct-Unique-Session-Id = "31b757fca2145e79"
Timestamp = 1227072287
Wed Nov 19 00:25:14 2008
Acct-Session-Id = "00000005"
User-Name = "cisco"
Acct-Authentic = RADIUS
Acct-Terminate-Cause = User-Request
Acct-Session-Time = 27
Acct-Status-Type = Stop
NAS-Port = 130
NAS-Port-Id = "tty130"
NAS-Port-Type = Virtual
Calling-Station-Id = "192.168.1.49"
Service-Type = NAS-Prompt-User
NAS-IP-Address = 192.168.1.201
Acct-Delay-Time = 0
Client-IP-Address = 192.168.1.201
Acct-Unique-Session-Id = "31b757fca2145e79"
Timestamp = 1227072314
[root@bertram ~]#
If there’s interest, I may expand on this later to include huntgroups, multiple RADIUS servers, using MySQL for accounting, or even through some LDAP and/or Active Directory authentication into the mix. If you’re interested, please leave a comment below


 LinkBack URL
LinkBack URL About LinkBacks
About LinkBacks





 riv-lvl=15
riv-lvl=15


